Remember when people stood on their soapbox and said that Microsoft should make things secure by default for everyone? That’s device encryption. If you’ve ever uttered the words “secure by default” you’re obligated to write Microsoft a thank you note now. They’ve taken the message on board so now you can expect even more unexpected security measures in your future. Meanwhile, we should learn what device encryption is, why it’s there and how it’s different than Bitlocker.
For the purpose of this blog, I’m going to assume that you’re an IT professional and since Bitlocker has been around since 2007, that’s 14 years, that you’re a Bitlocker expert by now. If you aren’t then, well this might sound harsh, but you might want to move from under that rock and come into the light.
What is device encryption?
Device encryption was introduced in 2013 in Windows 8.1. It was at this same moment that Microsoft started calling Windows a mobile operating system and treating its management as if it were. How does Microsoft manage security by default for a billion home users of Windows? One of the ways is with device encryption. You can think of device encryption as Bitlocker lite – automated. It is designed to be used on Home edition only. It has no management options because you can’t expect a billion end users to have the knowledge of how to manage encryption. Business devices should be running the Pro or Enterprise version of Windows and using Bitlocker. Bitlocker is encryption with options for professional IT to set and manage.
Why do we need device encryption?
Short answer: To protect your data from theft. When your data is stolen it is often used against you. For home users that usually means identity theft or impersonation. I didn’t look hard for any recent statistics, but in 2014 the FCC reported that over a million cellphones were stolen in the USA alone. Microsoft has to worry about what might happen to personal computers getting stolen world-wide. Suffice to say that the theft of computers should also be a very large number. There’s 1.3 billion Windows devices out there. If a tenth of a percent were stolen every year, that would be 1.3 million devices stolen probably with personally identifiable information on them. That’s a problem worth solving. This is why device encryption exists.
When you start up a new computer, device encryption is enabled by default. Encryption works with keys. One side of that key is your Windows hello authentication. The other side of it is stored on your computer. A backup is stored in the cloud. Remember, when you start up that new computer, you are prompted to create or logon to your Microsoft account. When you do so, your computer stores a copy of your encryption key in OneDrive. You can’t see it, but it’s there.
Why is your key backed up to OneDrive? Because it needs to be backed up somewhere and you and I both know that the home user isn’t going to do it themselves and even if that was an option, they would lose it. But storing that in the cloud is dangerous, you say? Well, in order to use that recovery key you have to have physical access to the computer. So a criminal, in order to gain access to the data on your stolen computer, has to know your logon information (Windows Hello) as well as have physical access to your computer. Snatch and run and encryption makes that computer useless to the hapless buyer of the hot goods, even if they put a new hard drive into it.
Does every computer support device encryption?
Every computer built to the Windows Hardware Certification Kit requirements supports device encryption. This is the way that all computers that have Windows pre-installed are supposed to be built in order to claim Windows compatibility. If your device doesn’t support device encryption then either it’s old, broken, or it wasn’t built correctly.
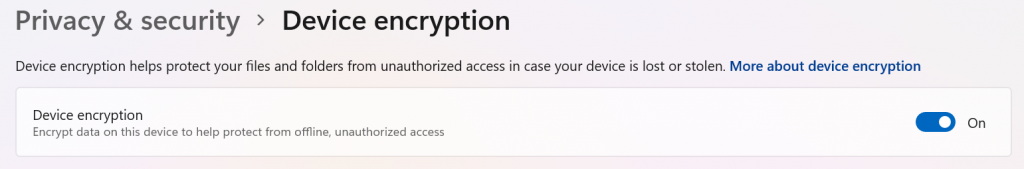
In Window 10 go to Settings/Update & Security. In Windows 11 go to Settings/Privacy & Security. Here you can see if device encryption is On or Off. If it’s Off, try turning it On. If your computer doesn’t support it you’ll get an error message telling you why. It is isn’t working, then mainly, your device probably doesn’t have a TPM or doesn’t support ConnectedStandby. Which means it wasn’t built to the hardware certification standards for Windows.
There are two halves to every encryption key. Where’s the other half?
The other half? That’s your Windows Hello login. When you start up your computer, before it boots, Windows gathers its part of the encryption key from the TPM. It then waits for you to enter the other half. Your half is your Windows Hello login. Whether that’s a PIN, a fingerprint or your face, that’s the other part of the encryption key that unlocks the encryption of your computer so it can be used. When the two come together, Windows is ready for work or play.
What happens if Windows can’t find its half of the key?
If the TPM goes bad or it can’t be accessed for some reason, then your computer will go into recovery mode and you will be provided with a link to your Microsoft account where the key can be retrieved from OneDrive. The options for recovering your device encryption key are the same as recovering a Bitlocker key because device encryption is the same thing as bitlocker without the professionally managed part.
I have recently seen people being puzzled and wondering how bitlocker happened on their computer. It’s a secure by default item. I have seen people screwing up their own security by not using a Microsoft account or not using Windows Hello and trying to make their computer dumb and their data less security by using local accounts. Computing has move on from those days. We need data privacy. We need data security. And for those things to happen for every home user, they need device encryption. Please don’t deprive them of the opportunity to be safe.
All we do is support IT professionals. Help for IT Pros, M365, Security community, MSP Legislation community, Kits, papers, courses, business consulting, peer groups and more. https://www.thirdtier.net




