Recently I posted that there was an important update for Outlook that needed to get installed. I sent a bunch of IT people scrambling and wondering how to do this efficiently. Let’s take a look at what Microsoft 365 has to offer.
But first, engage your users
I might be alone in this, but I like to engage the user population in their own security. Having them trained to occasionally respond to an emergency situation is not a bad thing. Our tools, whatever they are will never be as fast or add as much to security awareness as a direct interaction from the user.
When you encounter an important single CVE that needs to get installed right now. Engage the user community with a link and instruction set for installing the update. Do not abuse this, or you’ll end up in a “cried wolf” situation. But once or twice a year actually helps to reinforce that security is everyone’s responsibility.
Let’s automate
https://config.office.com has to be one of the least known and used portals in the entire Microsoft 365 suite. Too bad, because it contains some configuration and automation gems. Let’s see how we use it to automate Office updates.
Pre-requisite: Devices must be part of your device inventory. Join those devices to Azure AD!
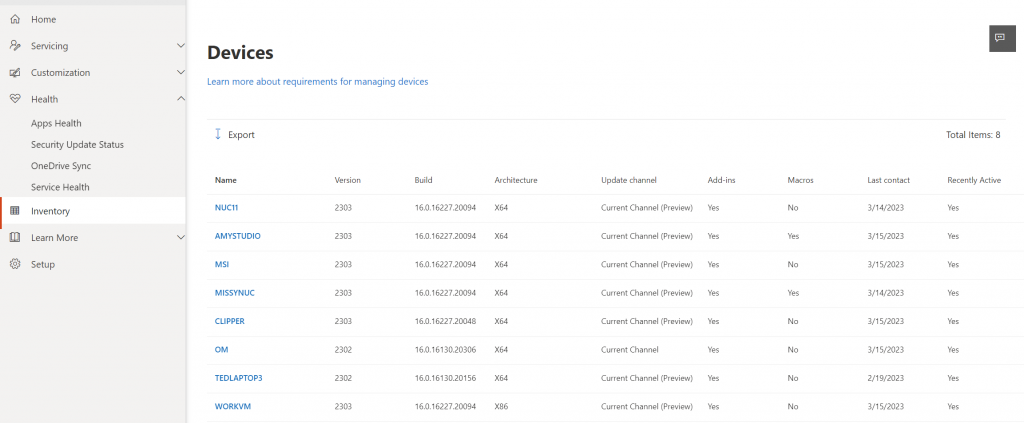
Step 1. Click on Inventory and see which devices are listed and what their current status is. If any are missing, go back and check their Azure AD join status before continuing. Any missing devices will be unaffected by the policies and monitoring that we’re going to setup.
Step 2. Click on Health and then Security Update Status. This is where we find some interesting information. I’ve highlighted certain parts with the red balls in the figure below.
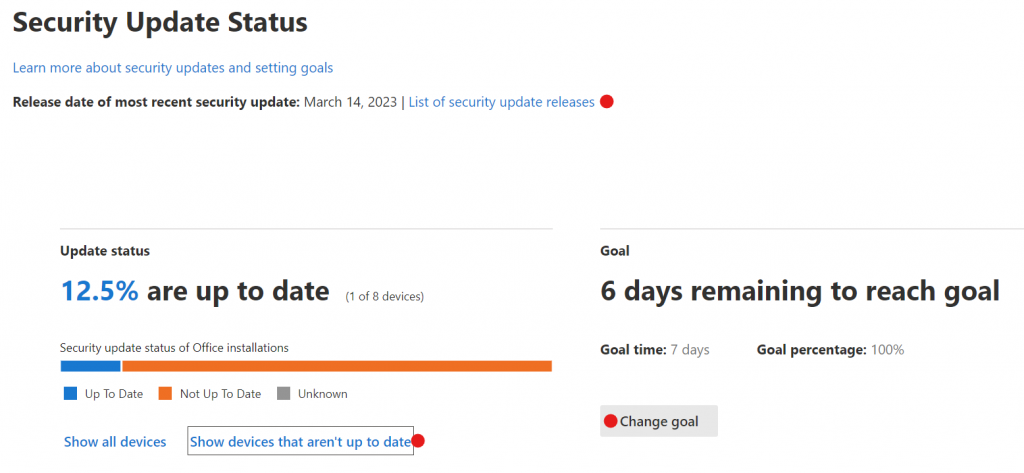
List of security update releases: From this screen we can click on List of security update releases which will give you the release numbers for each version of Office. You ‘ll need to know these numbers in order to tell how far behind a device might be. From here you can also see the individual updates that have been released for each sub-product.
Show devices that aren’t up to date: This is a list of devices that aren’t up to date or meeting the goal that you’ve set.
P.S. the numbers I’m showing you look terrible but that is because all of us are in the insider preview, which this system doesn’t know how to deal with. Those devices on Office Insider show up as not current due to their unique numbering system.
Change Goal: This takes you to a slider which allows you to set how many days are acceptable for the updates to be installed after release and the percentage that you consider acceptable. For small businesses, 7 days and 100% is common. If you have devices that you expect to be out of compliance you might want to consider another goal percentage.
Create an update policy for Office
Next, we’ll create our servicing profile for Office. Navigate to Servicing and then click the Settings tab. This is essentially a wizard which will step you through configuring your update policy for Office.
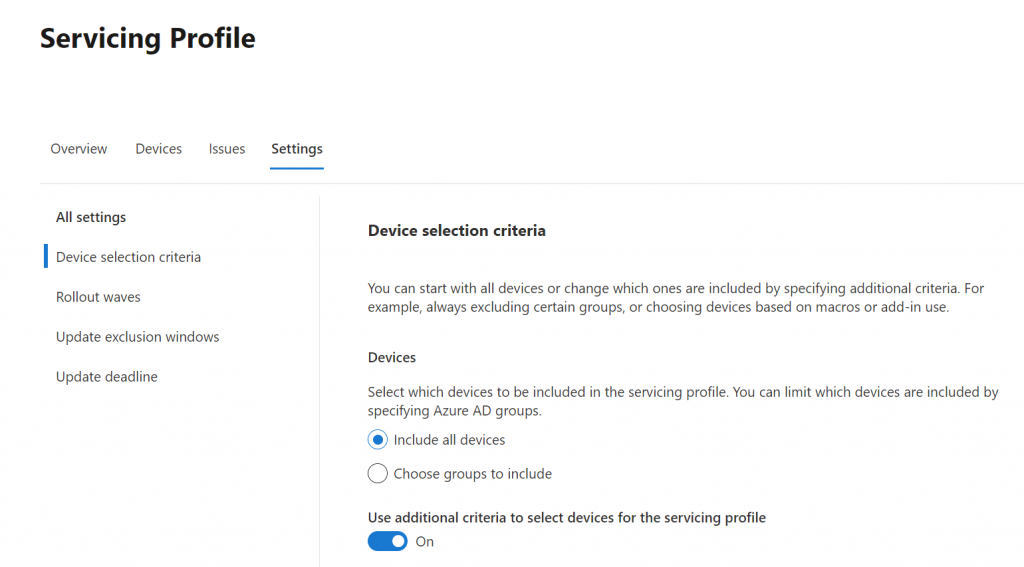
Device selection criteria: Choose to include all devices or only particular groups of devices that you want to manage office updates on. My advice is to select Include all devices and then use the additional criteria to narrow the selection if required. Turn on the slider for Use additional criteria to select devices for the servicing profile to see what options you have for selecting devices to manage.
Now you have the option to fine tune your managed devices by selecting to excluding specific device groups, select the Office channels that you want to manage, setting a limit on disk space so an update won’t fill someone’s hard drive, and choosing to exclude devices that use macros or add-ins. If there is going to be a problem with Office updates, it’s almost always Macro or Add-ins that are to blame. However, if you exclude them, they you’ll have to manage updates for those devices manually.
Rollout waves: In large environments you may want to limit the number of devices that update at the same time. You can do this if your devices are a member of an Azure AD for this purpose.
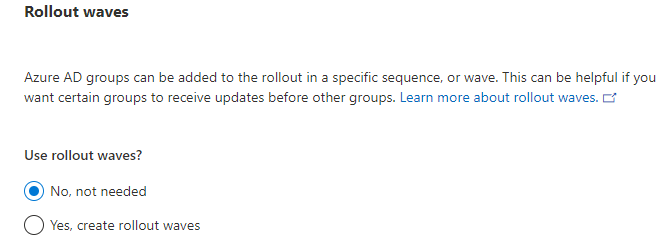
All you need to do here is select Yes, create rollout waves and then select the groups of devices and time frame between waves.
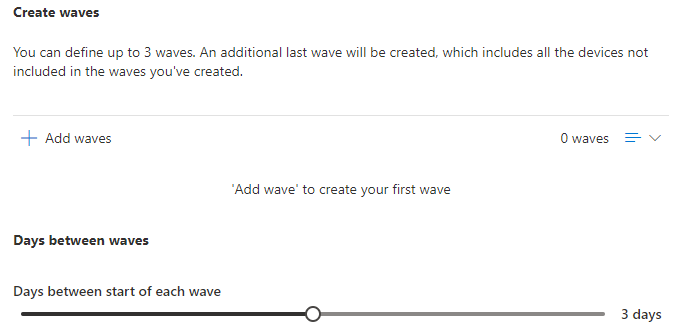
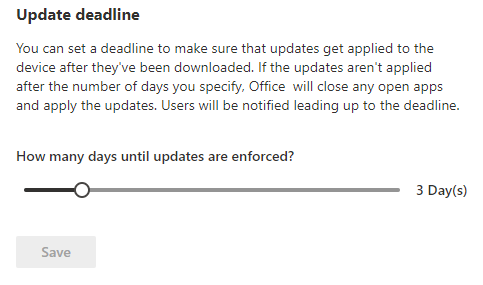
Update deadline: this is where you get to determine how many days are allowed before an update is enforced. Use the slider to set the value.
That’s it! Ignore everything else in this management console because it has been moved into Intune endpoint manager.
Intune endpoint manager Policies for Office Apps
This is well out of scope for this short blog post, but I did want to point out where the rest of your ability to manage Office has moved to.
Open https://endpoint.microsoft.com then navigate to Apps then Policies for Office Apps. This is not where you configure updates to Office, rather this is where you customize all of the others things about the Office applications.
Note: This page is incredibly slow! Just wait for it. It feels like the Office policy configuration server is housed under someone’s desk at Microsoft.
As an example, I have a policy here that provides additional file blocking for office applications. Essentially it keeps us from opening old documents since they have security limitations or often none at all.
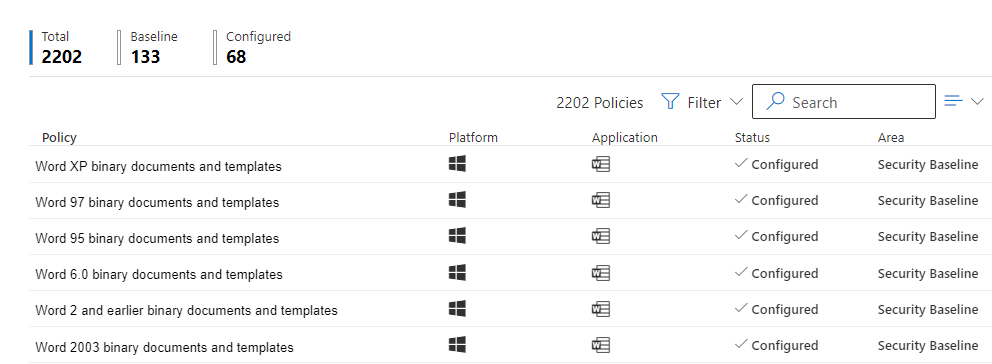
We can manage Office to great detail using Office app policies, including although in less detail, Office updates. Don’t let Office go unmanaged! It is a huge target.
If you like this content please join our Endpoint Manager, Lighthouse & Defender group. https://www.facebook.com/groups/endpointmanager
If you’d like to read more about configuring Intune endpoint manager, you can find more blog posts here.
All we do is support IT professionals. Microsoft 365 technical assistance, Super Secret News, Security community, MSP Legislation community, EndPoint, Defender and Lighthouse community, Peer groups, Kits, papers, Business consulting and more. https://www.thirdtier.net




3 thoughts on “How to manage Office updates with Microsoft 365”
Hello Amy,
First, thanks for being such an AWESOME resource! All your recognition is most certainly well deserved.
I am trying to set up a policy to update Office apps on devices (windows) and came across this article. I am having difficulty finding “Navigate to Servicing and then click the Settings tab”. I am thinking it’s just that in Microsoft fashion they moved things around or maybe I’m missing something in this blog. Can you point me in the right direction to configure/manage Office updates on my windows devices?
Kind regards,
Dan
Dan, Yes this has changed a lot. Microsoft introduced the concept of Cloud Update and changed where this is. It’s still in that portal but now its under Cloud Update, then the channel you’re using for office. For example, Current channel. Then move to the Settings tab to set the enforcement. See this picture. https://www.thirdtier.net/wp-content/uploads/2024/01/Screenshot-2024-01-16-114906.png
Thanks your support